Edge Security
Global Managed Microsegmentation Service
Managed Microsegmentation Service provides globally active organisations with tailored modular cybersecurity solutions –
with fast and secure entry into the world of zero trust microsegmentation.
We offer
Your solutions
Perfect for organizations who want consulting, design, visibility and initial deployment – and will operate internally.
- Visibility of the entire IT-inventory from day 1.
- 4x reduction in time to recover from Ransomware.
- Scalable segmentation maturity.
- Closes gaps in segmentation maturity without downtime and without network reconstruction.
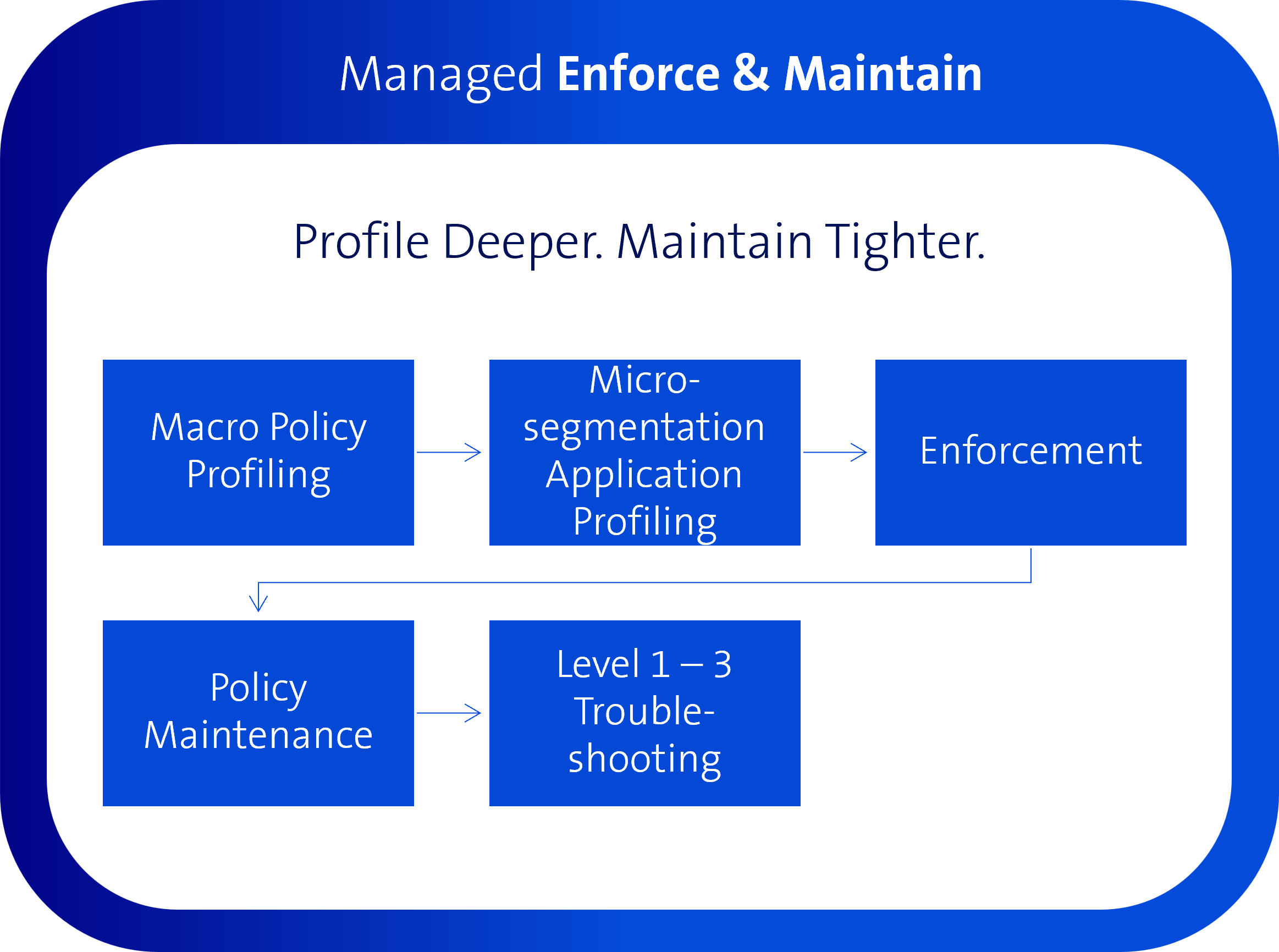
Perfect for organizations who want deeper profiling, ongoing operations, tuning, managed enforcement and support (L1-L3).
- Visibility of the entire IT-inventory from day 1.
- 4x reduction in time to recover from Ransomware.
- Scalable segmentation maturity.
- Closes gaps in segmentation maturity without downtime and without network reconstruction.
- Continuous, automatically controlled policy updates.
- Maintenance and Support (L1-L3).
Zero Trust Microsegmentation
Reduce Breach Impact
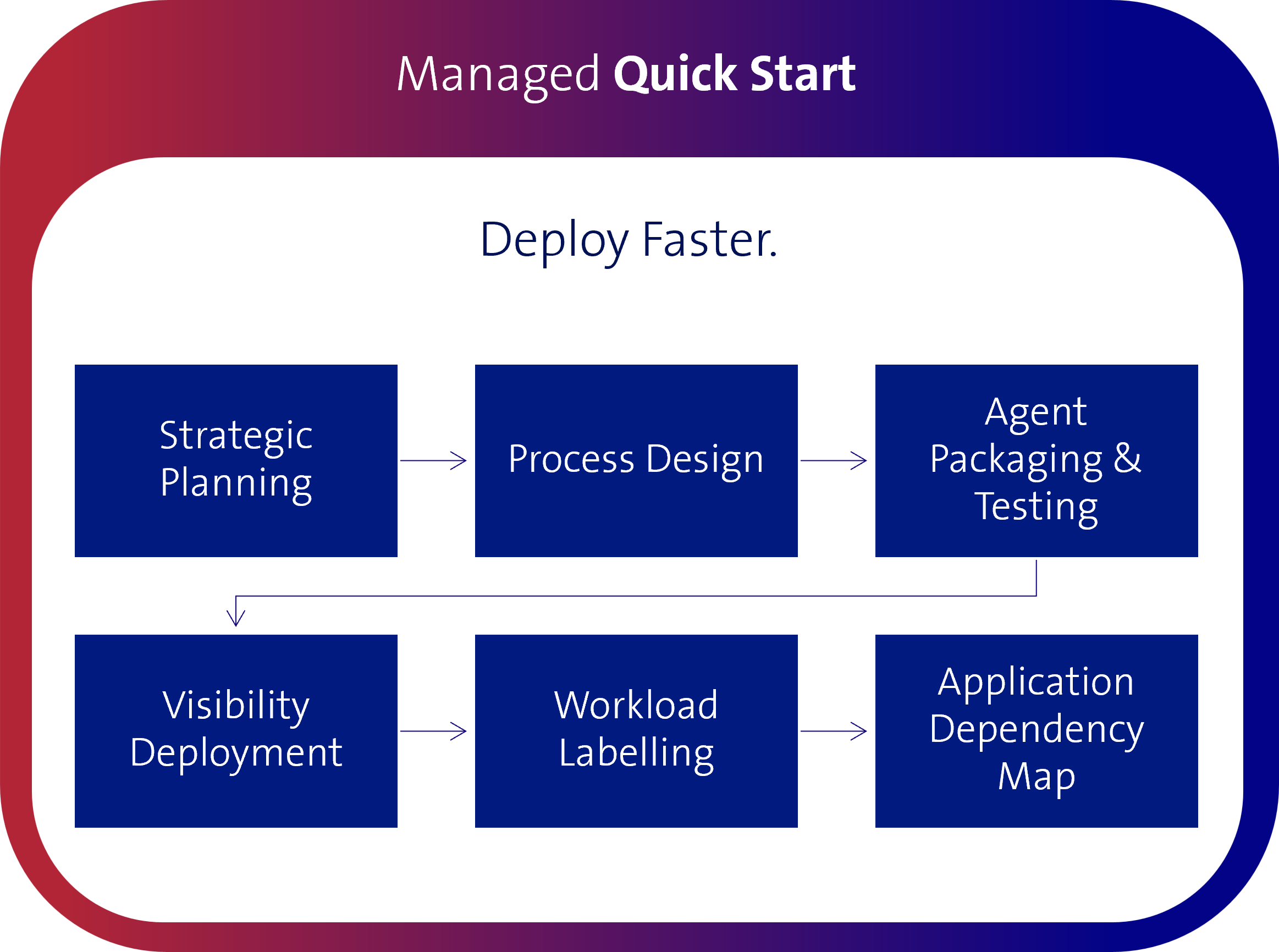
Deploy faster Microsegmentation from day one: plan, roll out, profile, implement. |
|
Profile deeper Microsegmentation that only allows for what your business needs and thus consistently minimises the area of attack. |
|
Maintain tighter Continuous monitoring and tuning throughout the entire application life cycle: monitor, maintain, readjust – so that segmentation remains reliably consistent. |
Cybersecurity challenges
Four times reduction in time to recover from Ransomware
Your benefits




Dynamic cyber resilience
Instead of a “regulatory paradox,” adopt a risk-based approach that focuses on real threats rather than just compliance with regulations. Microsegmentation offers development potential away from a static safety measure to a dynamic driver for cyber resilience, compliance and reduced security breaches..
Segmentation without downtime
Instead of isolated firewall rules, our solutions offer you microsegmentation tools that enable effective management of more mature, granular segmentation. Optimise your digital sovereignty by segmenting multiple asset types (data centres, networks, applications, IoT devices/machines, etc.) in parallel without operational downtime.
Cloud & on-premise compatibility
The clear and intuitive microsegmentation management platform supports automation, transparency, and guideline consistency, enabling unified segmentation across cloud and on-premise environments.
Workload-to-Workload
Rely on a workload approach, software-based segmentation, map-first transparency, simulation modes and fast containment. Isolate high-risk assets (such as IoT) and contain lateral network movement. Without network conversion or new network architecture, we guarantee a simple roll-out with low change risk./p>
Our exclusive partners


Answers to frequently asked questions
Can microsegmentation be operated without network modifications?
Short answer: Yes. Our partner Illumio applies workload-based implementation. No VLAN redesigns and no additional appliances are required. This reduces change risk and operating expenses, especially in hybrid data centre and cloud landscapes and OT-related environments.
How is compliance and auditability ensured?
Short answer: Through traceability, export capability and audit trails.
The policy and change history is fully traceable and can be exported for revision and audits. Mapping to requirements (e.g. ISO and NIST controls) can be documented on a project-specific basis. The separation of roles, duties and authorisations (SoD) is technically and organisationally feasible.
Who controls the policies and changes?
Short answer: The customer – with governance by Swisscom Broadcast
The role-based authorisation model (RBAC) is the handle for properly implementing policy management and follows the least privilege principle. The dual control principle applies to productive policy changes. An audit trail governs the seamless logging of changes (who/what/when) and can be exported for audits. Simulation modes (tests without enforcement) ensure change security before going live.
Can the partners (Illumio, ZT Solutions) access the customer’s content data?
Short answer: No.
The enforcement of segmentation policies is software-based on your workloads (agent/workload enforcement). No application and/or customer data is transferred to Illumio. Illumio does not require read access to databases, files or application content for policy enforcement.
How is the Cloud Act and the US addressed?
Short answer: Through architecture, contract and data minimisation.
In terms of architecture, the operating model is designed in such a way that no third-party access to content data is required. Your primary contractual partner under Swiss jurisdiction is Swisscom Broadcast. Data processing agreements (DPA/AVV) define the purpose, location and limits of data processing. Where telemetry/metadata is required, its scope, storage location (EU/CH options, if available) and storage can be defined contractually and technically restrictively.
What data does microsegmentation generate – and where is it located?
Short answer: Configuration, policy and metadata, no content data.
There are different types of data, including: Labels, guidelines, permitted and prohibited connections, technical function/role designations of workloads, ports and services. No payload or content data is generated.
You as the contractual partner decide where the data is located, within the scope of the operational options offered (e.g. EU or CH). The control processes are encrypted in transit (TLS) and retention periods as well as deletion and export processes are defined.