RaaS and “assume breach”
Why ransomware attacks are so successful
Ransomware is a lucrative business involving professional and specialised actors. Attacks on Swiss companies too are proving increasingly successful. There are various reasons for this.
Text: Andreas Heer, Picture: Adobe Stock, 11
Ransomware is a booming business. According to a report by the US Treasury Department, ransoms in the region of 600 million US dollars were paid in the first half of 2021 alone – more than in the whole of 2020. And because these criminal activities are so successful, cybercriminals continue to expand their business model.
Multiple methods of extortion with encryption and removal of data
Nowadays, ransomware attacks are more elaborate and go beyond simply encrypting the victim’s data and demanding ransom for its restoration. These attacks can often be repelled with ease by recovering the information from a backup. To increase their chances of success, cybercriminals now use up to four methods of extortion in their ransomware attacks:
- A company’s data is encrypted.
- The extortionist sets a deadline for payment. The data siphoned off before encryption is then published.
- To increase the pressure to pay the ransom, the extortionist also threatens to cripple the company structure using DDoS attacks.
- The extortionist publishes the name of the company on their leak site. In some cases, they even contact companies that are partners of their victim and inform them of the ransomware attacks. As well as causing reputational damage, this can also have legal and financial ramifications.
And because this business is so lucrative, numerous providers are eager to get in on the action. “We are currently tracking over 70 active ransomware groups,” says Stephan Rickauer, Head of the Computer Security Incident Response Team (CSIRT) for business customers at Swisscom.
Professionalisation with Ransomware-as-a-Service
And the attackers are now more professional than ever, dividing the individual steps up among various “professional groups”. The preliminary work, which usually involves capturing login details for the actual attack, is carried out by groups specialising in phishing. In turn, initial access brokers, as they are known, are responsible for spying out the captured, functioning logins. They then sell this data to the actual ransomware providers.
To gain initial access to a company's network, attackers do not necessarily exploit security loopholes in software. Instead, they use tried-and-tested methods, such as phishing emails or malware, e.g. the now discontinued TrickBot or increasingly BazarBackdoor, to obtain valid login details. These then open the doors to the company, for example, via remote access or VPN access without two-factor authentication. Thomas Röthlisberger, Head of the Red Team at Swisscom, is familiar with these attack techniques from his own work: “Ransomware attackers are opportunistic. They attack where they see an opportunity to do so, i.e. when an access point can be exploited.” The actual ransomware, for example “Conti”, is installed afterwards following a successful breach.
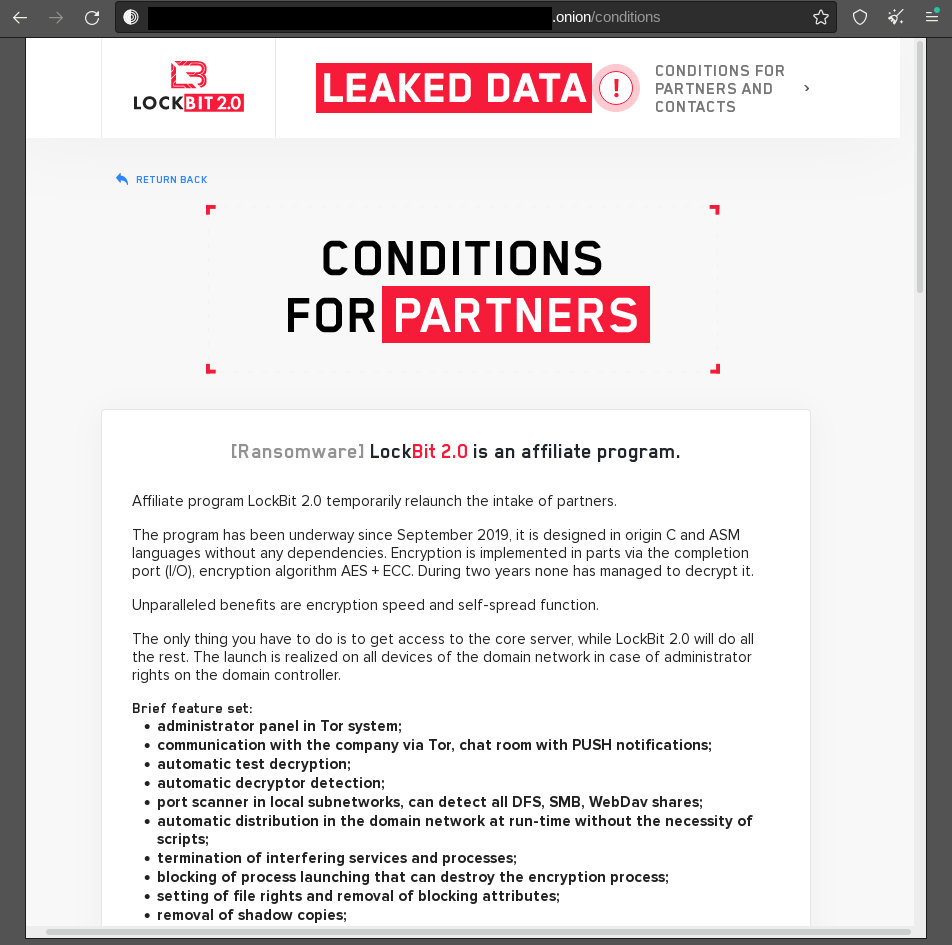
The group behind LockBit 2.0 actively looks for “affiliates”, i.e. partners to launch ransomware attacks.
But it’s not always the providers themselves who launch an attack. Some ransomware developers provide their tools to other criminal groups as a service and earn commission on the ransom. This Ransomware-as-a-Service approach, e.g. with BlackCat/ALPHV or LockBit 2.0, is comparable to Software-as-a-Service. This means that no specialist knowledge is needed to launch a ransomware attack, but rather, the right amount of criminal energy. This is another sign of the market’s profitability and also suggests that the number of attacks will continue to rise.
“Assume breach” as a starting point
For specialists like Röthlisberger and Rickauer, it is clear that ransomware is the greatest cyber threat facing companies and organisations in the majority of sectors. Investing in technical development is a worthwhile endeavour for attackers. Following prosecution and the subsequent disbandment of a criminal group, there is never any shortage of successors to pick up where these criminals have left off under a new name.
That is why successful attacks regularly make the headlines in Switzerland as well. “Many companies view ransomware as purely a technical problem that IT needs to take care of,” explains Rickauer. Accordingly, there is a lack of strategic measures such as an emergency plan. Rickauer describes the situation as follows: “When targeted by an attack, companies first need to learn how they can negotiate with the extortionists or how they can purchase a large quantity of Bitcoins at short notice in order to still pay the ransom, despite recommendations to the contrary.” Companies would therefore gain a lot if they were in a position to deal with ransomware attacks at a strategic level within the context of risk or business continuity management. Because a ransomware attack today always poses a crisis for the affected company.
In Röthlisberger’s experience, security monitoring to detect attacks at an early stage is often lacking: “Companies have to assume that an attacker will be successful at some stage or has already penetrated the network, i.e. ‘assume breach’.” Once the attackers are inside the company network, they can exploit vulnerabilities in the defences, explains Röthlisberger: “Cybercriminals often use stolen login details and gaps in Microsoft’s Active Directory in order to penetrate deeper into the company network.” This way, the intruders can get their hands on advanced access rights and in the ideal scenario (from the attacker’s perspective), take on the role of domain administrator and encrypt all important company data and systems with ransomware.
Ransomware as an issue for the management board
Like Rickauer, Röthlisberger urges management boards to tackle the subject of ransomware in the context of risk management – by taking concrete measures to improve overall security. One potential measure would be to set up a Security Operation Centre (SOC) with a CSIRT in order to detect and stop attacks and develop company defences using simulated Red Team attacks.
However, those responsible would need an overview of the entire system network to be able to quantify the risk. “This is often a challenge,” admits Röthlisberger. The complexity of IT architectures is regularly cited as one of the main reasons for this. The log4j security vulnerability (“log4shell”) clearly demonstrated this problem last December: many companies have no idea about the types of security loopholes that might be lurking in certain libraries. Or as Rickauer puts it: “These days, best practices rarely work as planned in the complex world we live in. Every phenomenon is different.” However, due to the real threat posed by ransomware, companies have no option but to take appropriate defensive measures.
More on the topic:

