First aid for a hacker attack
Companies are constantly being attacked by hackers. If data is stolen, the correct actions must be carried out as quickly as possible. One scenario shows how to limit the damage.
Companies are constantly being attacked by hackers. If data is stolen, the correct actions must be carried out as quickly as possible. One scenario shows how to limit the damage.
4 min
“The website is not available” – this is the alarm SMS received by Arno P. in the middle of the night. As he is responsible for the IT of an online retailer, Arno P. gets up and logs into the system in the usual way to see what the problem is. “This could really wait until the morning,” he thinks to himself, because hardly anyone uses the Swiss web shop during the night.
But when he sees the traffic figures he can hardly believe his eyes – there’s an inexplicably high level of data traffic on the servers. Evidently attackers are using a multitude of automated attacks in an attempt to make the website inaccessible.
However, when he examines the logs on the servers he discovers that customer data is also being stolen at the same time. The attack on the website might only be a distraction. He is unable to shut down individual servers, and he is unsure whether he should start blocking the data theft himself, or even how to do this.
An emergency plan is indispensable
The incident described can either be a catastrophe for the company, or it can get off lightly. In the optimum scenario, an emergency plan informs Arno P. what to do. He calls the support number at Swisscom, whose services and infrastructures are used by the company. Swisscom is up to speed and has already blocked a number of areas in which suspicious activities were detected.
“This is a DDoS attack,” says the responsible member of the security team. “We were able to filter out the malicious network traffic, and the service will be available again soon.” However, the hackers also managed to exploit a weakness in a database and copy customer data.
The first thing we want to do is stop these activities(opens in new tab). Only then do the security specialists use the log files to try to find out how the attackers were able to access the sensitive data.
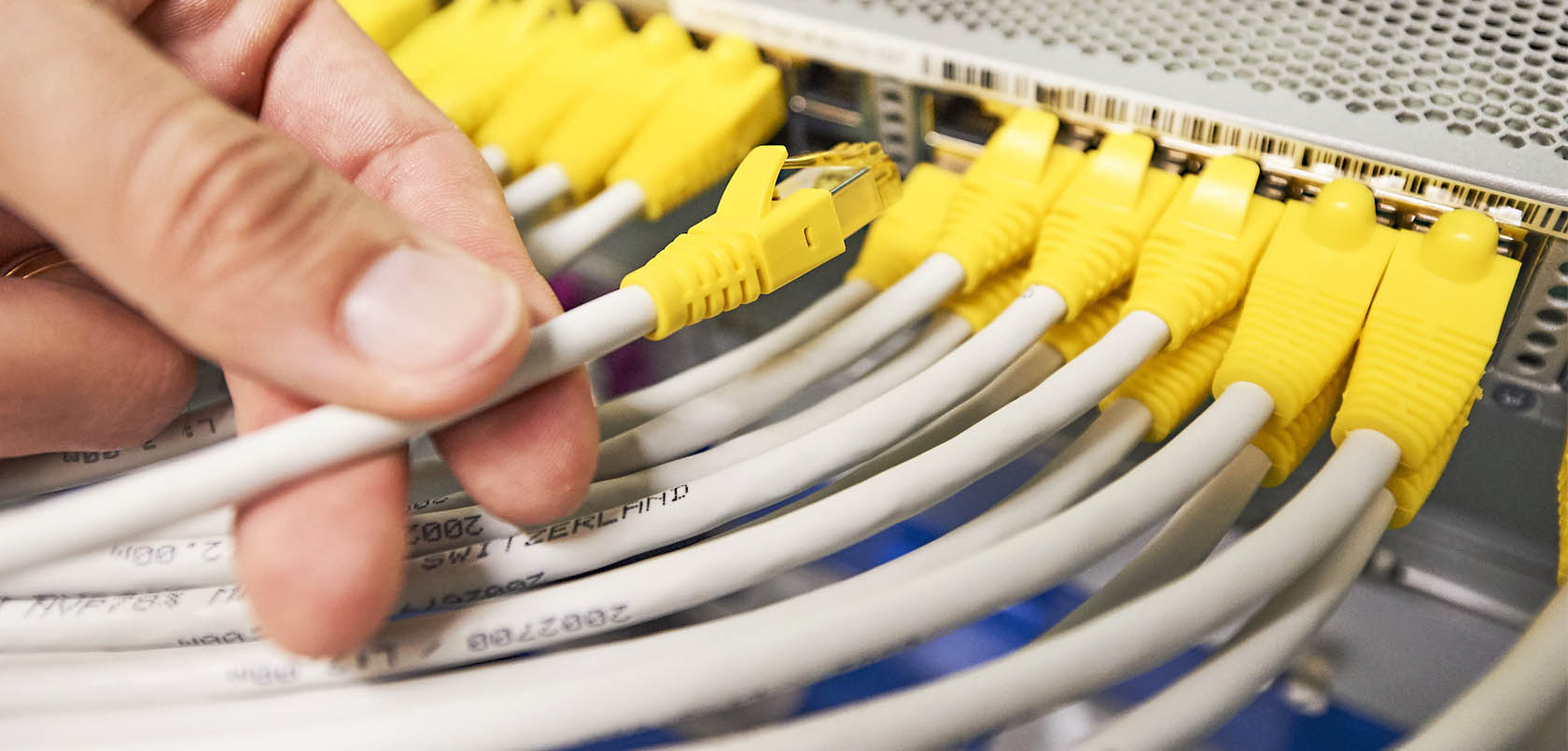
Because the company is not using all of the services at Swisscom, the goal is now to limit the damage on the company’s own servers. So Arno P. goes into work. There he pulls the ethernet plugs of the servers in accordance with the instructions in his emergency plan, but he does not shut down the computers, in order to be able to reconstruct any potential manipulation later. “The memory can tell us a lot about the nature of the interference with the system,” says Lorenz Inglin, Head Cyber Defense at Swisscom.
The subsequent analysis of the log files will reveal that the attacker got into the system via a weakness in the application (using an “SQL injection”). Swisscom’s forensic team now has the task of preserving evidence and finding out who could be behind the attack. They have to analyse where the attack came from, what data was stolen and how significant the damage is. It is equally important to block the communication channels for the attackers and repair the weakness in the application. The employees and customers also have to be told what they need to do. An official statement should also be prepared for the media and customer services.
In an emergency, the experts from Swisscom’s Cyber Security Incident Response Team (CSIRT) are by your side, providing quick, professional support.
Emergency plan: actions following an attack
Even with the best preventive actions, hackers may still be able to steal data using a wide range of attacking methods. After an incident is detected, every second counts. Swisscom’s Computer Security Incident Response Team deploys the following actions to defend against threats:
- Evaluate the available information on the incident. What is going on? Is it necessary to send a Swisscom team to the company?
- Initiate immediate actions (stop activities and evaluate the extent of the damage and the data losses)
- Find the cause of the problem
- Initiate actions to contain / remove the problem
- Improve the protection and identify comparable problems
- Restoring, validating, monitoring
- Preserving evidence (source of attacks, potentially for legal purposes)
- Debriefing, documentation, implementing corrective actions
Costly aftermath of an attack
After the initial actions have been carried out, the concern is now to limit the damage as far as possible. It is very difficult to determine the extent of the actual damage. Financial damage can occur directly or indirectly. Potential factors are:
- Internal workload to remove problem and restore systems
- External forensic workload and restoring leased systems
- New security measures
- Reputation: damage to image, loss of customer trust, drop in share price
Current threats to companies
Hackers use a wide range of methods to access sensitive data such as customer information, credit card details, passwords etc. Lorenz Inglin: “Attacks are made on a daily basis and we are permanently on alert, trying to detect and repel such attacks.”
“We are continuously monitoring our networks, looking for unusual occurrences. For example, we detect and block phishing websites every month,” says Lorenz Inglin.
At present, companies are mainly exposed to the following threats:
- Phishing
- DDoS attacks (disabling of services and websites)
- Ransomware (data encryption followed by blackmailing)
- Social engineering (using tricks to obtain data and passwords). Example: “Fake President Fraud”: A scammer pretends to be a member of the company management and gets employees to make bank transfers.