Security- and Compliance-Monitoring with Audit Guard
Audit Guard brings transparency to handling sensitive data
There is often a lack of transparency in dealing with sensitive data: who did what, when and where?
However, this transparency is just as important for proving compliance as it is for data theft. Companies therefore need a tool to log any access to sensitive data and alert them to breaches.
When is it the right solution?
Despite heterogeneous, complex infrastructures, companies need transparency when it comes to processing of sensitive data. Legal requirements, regulations and compliance demands mean that IT managers must be able to prove that personal customer information, health data and other personal details have always been handled correctly.
The first step
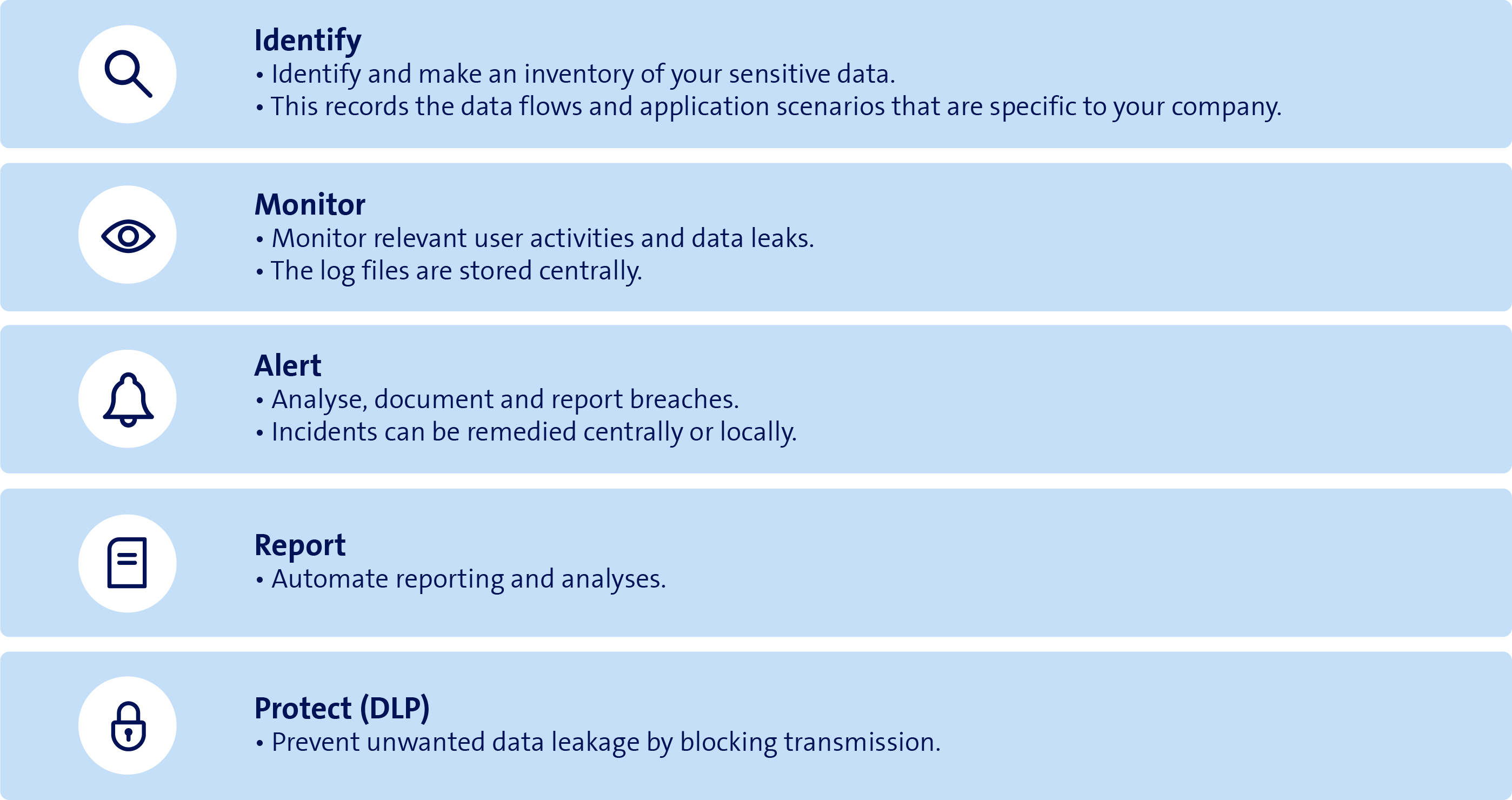
Audit Guard overview
The Swisscom I-MARS security concept
The Swisscom I-MARS security concept is designed to facilitate transparency, measurability and comprehensive control for protecting sensitive data. It includes Audit Guard and the Data Loss Prevention service that prevents unwanted data leakage. Swisscom also uses these services to handle sensitive data. Would you also like to control sensitive data access and handling in your company?